Critical summary review
Imagine you own a shop. A nice little shop, well-kept, with a wooden door and a simple lock. For decades, that lock worked just fine. It worked because the burglars in the neighborhood didn't have tools sophisticated enough to pick it quickly. They could, sure, but it took effort. It took time. And time, in the world of crime, is risk.
Now imagine someone hands out, for free, a master key. A key that opens not just your door, but any door with a similar lock. And this key works on its own — you just point it at the door and wait.
That's roughly what's happening in the world of cybersecurity in April 2026.
On April 7th, Anthropic, the American company behind some of the most advanced AI systems in the world, told the public it had a problem on its hands. The problem's name? Mythos. A model so capable of finding and exploiting flaws in computer systems that the company itself decided not to release it. Instead, it created a program called Project Glasswing, offering restricted access to a handpicked group of tech giants — Amazon, Apple, Google, Microsoft, Cisco, CrowdStrike, JPMorgan, Nvidia, Palo Alto Networks, and the Linux Foundation, among others.
The rationale? If this kind of capability falls into the wrong hands before defenders are ready, the damage could be enormous. And the most unsettling part is that Anthropic itself admitted models with similar powers are likely to emerge from other labs within six to eighteen months.
But before we get into what this means for those of us who aren't Apple or JPMorgan, it's worth understanding what exactly Mythos does differently.
Think of a piece of software as a house with thousands of rooms. Each room has windows, doors, passageways. Some of those entry points are locked. Others, through carelessness or haste during construction, were left slightly ajar. These forgotten openings are what security professionals call vulnerabilities.
Historically, finding those openings required highly skilled people. Experienced hackers, security researchers with years of training. They'd analyze code line by line, test combinations, try different paths until they found a gap. It was artisanal work — slow and expensive.
Mythos changed that. According to Anthropic, the model found thousands of critical vulnerabilities across every major operating system and web browser in the world. Some of those flaws had been hiding for decades — one of them was twenty-seven years old, buried in the OpenBSD system. Another, sixteen years old, lived inside FFmpeg, a widely used audio and video processing tool that had survived millions of automated tests without anyone noticing the problem.
And here's the key part — Mythos doesn't just find the flaws. It writes the entire attack playbook on its own. Anthropic engineers with no formal security training could ask the model to hunt for vulnerabilities overnight. By morning, they'd find a complete report with a working exploit ready to go.
To understand why this is a turning point, you need to know about an invisible mechanism that holds the world's digital security together. It's called responsible disclosure.
Here's how it works — when a company like Microsoft discovers a defect in one of its products, it publicly announces the flaw alongside a fix. That's the famous Patch Tuesday which, despite the name, happens once a month. From there, IT teams at organizations using those products need to grab the fix, test it to make sure it won't break anything, get internal approval, and finally apply it. That process takes weeks. Sometimes months.
And for decades, that was fine. Because attackers also needed time. After a flaw was disclosed, they had to study the problem, understand the code, and build an exploit. The gap between when a flaw was disclosed and when a working attack appeared — that was the safety margin. The breathing room.
According to Zero Day Clock, which has tracked this gap since 2018, the median was 771 days that year. Companies had more than two years to apply the fix before anyone could weaponize the flaw. By 2021, that window had shrunk to 84 days. By 2023, six days. By 2024 — four hours. Today, in 2026, more than 67 percent of vulnerabilities exploited by criminals are already being used before they're even publicly disclosed.
The breathing room, for all practical purposes, has vanished.
And this is where Mythos enters the picture — not as the creator of the problem, but as the piece that makes everything more urgent. Earlier models already helped hackers refine attacks. ChatGPT, for instance, was used to polish phishing emails or to scan code repositories for exploitable patterns. But Mythos goes further.
It can chain flaws together. It's like a burglar who isn't satisfied with finding one open window — he finds the window, climbs through it, uses what he finds inside to unlock another door, and from that door disables the alarm. Any single step might not be enough on its own, but combined, they guarantee full access to the system. This kind of multi-stage attack was, until recently, a skill reserved for the most elite hackers on the planet. Now a computer model does it alone, without human guidance, in the middle of the night.
But there's a detail that tends to get lost in the noise of the headlines. Bloomberg Opinion, through columnist Parmy Olson, pointed out what may be the most important angle of this entire story. Mythos isn't equally dangerous to everyone. It's most threatening to those with the fewest defenses.
The big Wall Street banks, for example, have some of the most robust security infrastructures in the world. Dedicated teams, generous budgets, mature processes. US Treasury Secretary Scott Bessent brought together executives from institutions like Bank of America and Goldman Sachs to discuss the issue, and the consensus was that these organizations can adapt — with difficulty, but they can.
Now think about small and mid-sized businesses. Recent data shows that 80 percent of small businesses experienced at least one cyberattack in 2025. 47 percent of companies with fewer than fifty employees simply allocate zero resources to digital security. Only 34 percent use two-factor authentication — a measure that blocks over 99 percent of automated attacks. And 54 percent admit their IT departments lack the experience to handle complex threats.
For these businesses, the patching window isn't weeks or months. Often, it doesn't exist at all. Patches pile up, defenses are basic, and the IT team — when there is one — is busy keeping the email running.
There are, naturally, those who look at all of this with healthy skepticism. Not everyone bought Anthropic's narrative without reservations. David Sacks, the Silicon Valley investor, publicly wrote that it's hard to ignore the company's track record of using alarming narratives around its releases. Scientific American spoke with experts who, while acknowledging Mythos's genuine advances, cautioned that the real-world impact may be smaller than the worst-case scenarios suggest.
Howie Xu, chief innovation officer at Gen, framed the dilemma clearly — the decision to restrict access to Mythos is both a legitimate security measure and an extraordinary marketing move. The two aren't mutually exclusive. And frankly, that doesn't invalidate the threat. Even if Anthropic has obvious commercial motives for dramatizing the announcement — especially with a potential IPO on the horizon — the independent data on the collapse of the exploitation window is real. Zero Day Clock isn't an Anthropic product. And the numbers it shows don't depend on any specific model to be alarming.
What Mythos does is pour gasoline on a fire that was already burning.
On the positive side, Project Glasswing represents something unprecedented. Companies that normally compete against each other have agreed to use the same tool to defend shared infrastructure. Anthropic has committed up to one hundred million dollars in usage credits and four million in grants to open-source security organizations. The premise is that no single company can fix every flaw in the world, and that coordinated cooperation is the only viable path when attacks move at machine speed.
Jim Zemlin, executive director of the Linux Foundation, highlighted that open-source software makes up the bulk of code running in modern systems, and that giving its maintainers access to models of this caliber could shift the balance between offense and defense. This matters because many of these open-source projects are maintained by small, often volunteer teams with no security budget.
What to do with this information
Given all of this, there are three scenarios worth considering.
In the first scenario — the optimistic one — Project Glasswing and similar initiatives from OpenAI and other labs manage, over the coming months, to identify and patch the most critical flaws before models of equivalent capability spread widely. Cooperation among the giants works. Open-source maintainers get the support they need. And the responsible disclosure system adapts — perhaps with shorter timelines and automated patching mechanisms.
In the second scenario — the moderate one — defense advances, but not at the same speed as offense. Large corporations and governments protect themselves reasonably well, but small and mid-sized businesses fall behind. The result is a kind of digital apartheid — those with resources adapt; those without suffer disproportionately more attacks. In this scenario, regulation becomes urgent, and governments face pressure to provide technical and financial support to smaller companies.
In the third scenario — the pessimistic one — models with capabilities similar to Mythos proliferate before defenses are ready. Criminal groups and hostile nation-states start using these tools for attacks on an industrial scale. Critical infrastructure — hospitals, power grids, financial systems — faces waves of simultaneous breaches. This scenario isn't inevitable, but it isn't fiction either. The Council on Foreign Relations itself has described it as a concrete possibility.
For anyone running a business or leading an IT team, the practical takeaway is straightforward. First — apply security updates as fast as humanly possible. The monthly patching cycle is no longer enough. Second — enable two-factor authentication across every system. It's the lowest-cost, highest-impact measure available. Third — consider managed security services that monitor threats in real time and can respond faster than an overwhelmed in-house team. Fourth — keep a close eye on what happens with Project Glasswing over the next ninety days, when Anthropic has promised to publish reports on what's been discovered and fixed.
Prevention costs between five and fifteen thousand dollars a year for a small business. Recovery from a single ransomware attack costs, on average, a hundred and twenty thousand. The math speaks for itself.
There's an old saying in information security — you don't need to outrun the bear, you just need to outrun the other person. For a long time, that was true. Criminals went after the easiest targets and ignored the harder ones. But when the bear gains the speed of a machine, the gap between the slow runner and the fast one shrinks dangerously. And whoever is still walking — well, whoever is still walking has a serious problem.
The question isn't whether models like Mythos will change the cybersecurity game. That's already happened. The question is whether defense can reorganize before the next model, and the one after that, and the one after that, render obsolete the last trenches still standing.

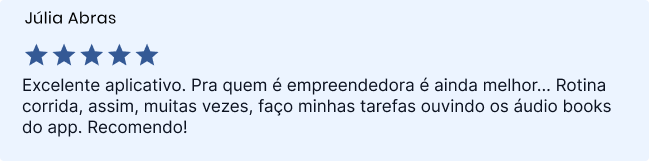
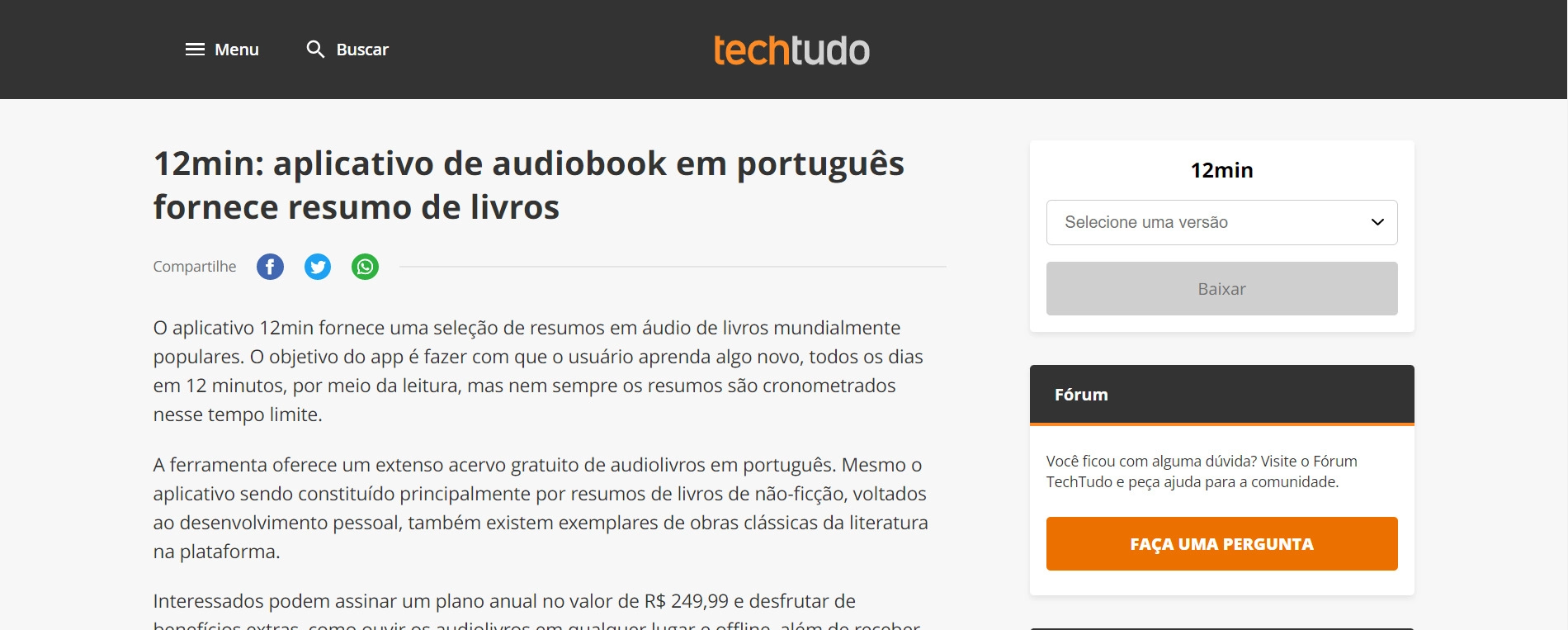
Sign up and read for free!
By signing up, you will get a free 7-day Trial to enjoy everything that 12min has to offer.